To safely manage your DeFi funds, use multisignature wallets requiring multiple approvals for transactions, which makes exploits much harder. Store private keys offline on hardware wallets to reduce hacking risks. Limit bridge transfers and choose reputable, audited cross-chain solutions to prevent vulnerabilities. Always keep your software updated and never share your seed phrases. Applying these tools together creates a solid defense system—continue exploring ways to enhance your crypto security even further.
Key Takeaways
- Use multisignature wallets requiring multiple approvals to prevent unauthorized transactions and enhance security.
- Store private keys offline in hardware wallets to reduce exposure to hacking threats.
- Limit transfer amounts via cross-chain bridges and verify their security audits before use.
- Regularly update security tools, avoid sharing private information, and stay vigilant against phishing attempts.
- Combine hardware wallets, multisig setups, and continuous monitoring for comprehensive DeFi asset protection.

Decentralized finance (DeFi) has revolutionized how we manage and access financial services, but it also introduces new security risks. As you explore DeFi platforms, you need to be aware that your funds can be vulnerable, especially when using tools like cross-chain bridges or storing assets in hot wallets. Cross chain bridges are essential for transferring assets between different blockchains, but they can also be targeted by hackers. If a bridge isn’t properly secured, it could be exploited, leading to significant losses. To mitigate this risk, you should only use reputable bridges with strong security audits and consider limiting the amount of funds you transfer through them.
Hardware wallets are another crucial security tool. Unlike software wallets, which are connected to the internet and more vulnerable to hacking, hardware wallets store your private keys offline. When you use a hardware wallet, even if a malicious actor manages to compromise your device or your computer, they won’t be able to access your private keys or steal your funds. This extra layer of security is vital when dealing with large sums or valuable assets in DeFi. Always ensure your hardware wallet is kept in a safe place and that you purchase it from official sources to avoid tampered devices.
In addition to using hardware wallets, employing multisignature (multisig) wallets can greatly enhance your security. Multisig requires multiple private keys to authorize transactions, making it much harder for hackers to drain your funds. For example, if you set up a multisig wallet that requires three out of five keys to approve a transfer, a single compromised key won’t be enough for unauthorized access. This setup acts as a safeguard, especially if you’re managing large amounts in DeFi. Combining multisig wallets with hardware wallets creates a robust defense system. You can store some keys offline on hardware wallets and keep others in secure locations, reducing the risk of total loss. Furthermore, ongoing monitoring of AI behavior is crucial to identify potential vulnerabilities or suspicious activities in your security setup.
It’s also essential to stay vigilant about updates and security practices. Regularly update your hardware wallets and ensure your cross chain bridges are from trusted sources. Never share your private keys or seed phrases, and be cautious of phishing attempts that try to trick you into revealing sensitive information. By combining the use of cross chain bridges carefully, securing your assets in hardware wallets, and implementing multisig wallets, you set a strong foundation for safer DeFi interactions. These tools help you protect your assets against common vulnerabilities, giving you peace of mind as you navigate the decentralized financial ecosystem.

TANGEM Wallet Pack of 2 – Secure Crypto Wallet – Trusted Cold Storage for Bitcoin, Ethereum, NFT's & More Coins – 100% Offline Hardware Wallet
THE HIGHEST LEVEL OF SECURITY: Tangem Wallet generates the private key that never leaves the card. Your crypto…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Do Multisig Wallets Compare to Hardware Wallets for Security?
Multisig wallets offer better multisig security by requiring multiple signatures for transactions, reducing the risk of single-point failure. Hardware wallets, on the other hand, provide strong security by storing your private keys offline, protecting against online attacks. While multisig wallets excel in collective control and redundancy, hardware wallets are ideal for individual users seeking robust offline protection. Combining both enhances your overall security, making your funds much safer.
Are There Specific Defi Platforms With Built-In Multisig Features?
Many DeFi platforms now incorporate built-in multisig features, helping you protect funds despite potential smart contract vulnerabilities. Platforms like Gnosis Safe and Argent offer user-friendly interfaces, making multisig management easier. These designs minimize user errors and improve security, even if the underlying smart contracts have vulnerabilities. By choosing platforms with integrated multisig, you enhance your funds’ safety and streamline multi-party approvals, reducing risks associated with complex DeFi transactions.
Can Multisig Wallets Be Hacked or Compromised?
Multisig wallets can be hacked or compromised if you’re not careful. Multi signature vulnerabilities, like compromised private keys or weak wallet encryption, pose risks. Even with multisig, if one key is stolen or exposed, your funds could be at risk. Always use strong wallet encryption, keep private keys secure, and consider multi-layer security measures to reduce these vulnerabilities and protect your assets effectively.
What Are the Best Practices for Managing Multisig Key Shares?
You should carefully plan key distribution by splitting access controls among trusted parties, ensuring no single person holds complete control. Use secure methods like hardware wallets for key shares and store them separately in safe locations. Regularly review and update your multisig setup, and limit access to essential members only. Clear protocols for key sharing and revocation help prevent unauthorized access, maintaining your funds’ security.
How Do I Recover Funds if One Multisig Key Is Lost?
Losing a multisig key is like losing a vital piece of a puzzle, but you can still recover your funds. You should have a solid key management plan, including secure backups stored in multiple locations. To recover, use your backup key shares for key recovery, ensuring your remaining keys are intact. Regularly review your multisig setup to prevent future issues and maintain control over your funds.

TANGEM Wallet Pack of 2 – Secure Crypto Wallet – Trusted Cold Storage for Bitcoin, Ethereum, NFT's & More Coins – 100% Offline Hardware Wallet
THE HIGHEST LEVEL OF SECURITY: Tangem Wallet generates the private key that never leaves the card. Your crypto…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
Using tools like multisig wallets and other security measures might seem complex at first, but they’re essential for protecting your funds. Think of multisig as a secure vault requiring multiple keys—without all of them, your assets stay safe. By embracing these safety tools, you reduce the risk of hacks or mistakes. It’s like having multiple locks on your door; it’s worth the extra step to keep your investments secure.
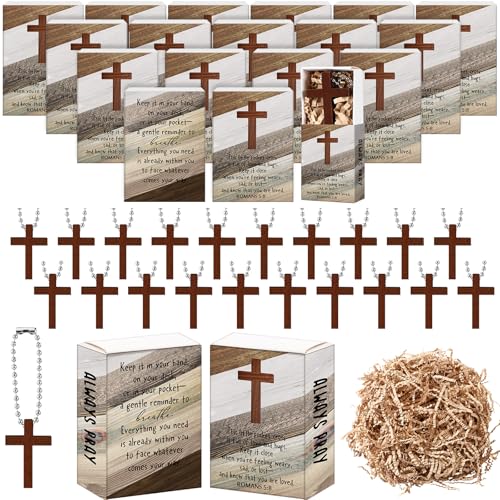
Tondiamo 36 Set Christian Gifts Wooden Cross Charm Religious Hanging Favors Cross Keychain Small Wooden Crosses Pocket Prayer Box Father's Day Gifts for Men Church DIY Craft
Package Contents: this curated collection of wooden cross keychain sets, each elegantly paired with its own chain, boasts…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Hotop 2 Pcs Crypto Wallets and 1 Pcs Metal Plate Marking Pen, Cryptocurrency Wallets for Hardware Cold Backups Seed Storage for Bitcoin Compatible with Bip39 Hardware(Black)
Quality Materials: these crypto wallets are made of aluminum with a melting point of over 2500 degrees Fahrenheit…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.









